As cybercrime increases, we all need to be doing more pre-emptive pushback on these activities.
One of the weapons in this ongoing battle is two-factor authentication.
Just what is it and how can I implement it if I need to?
What is it?
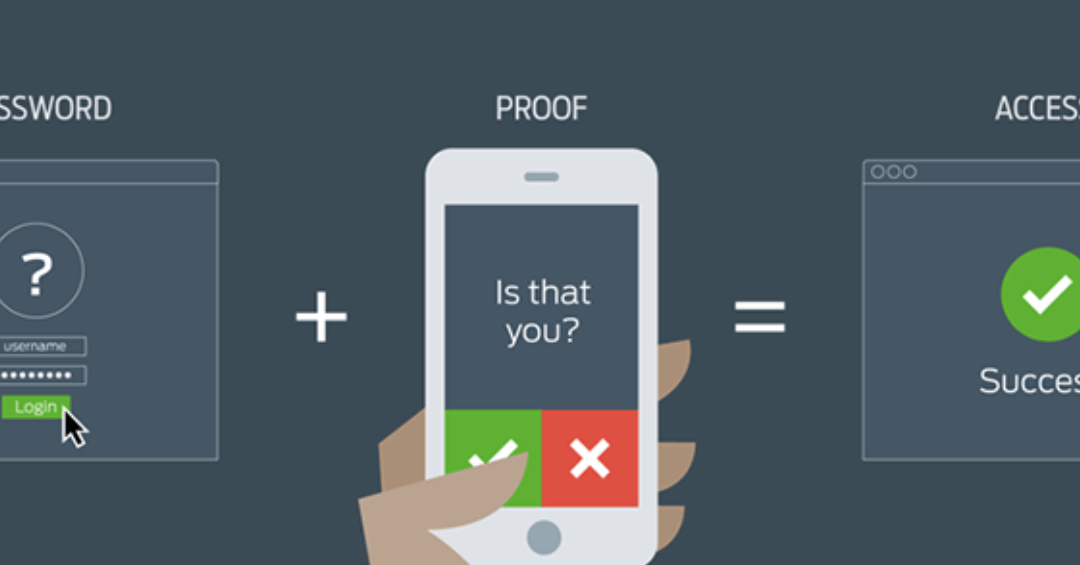
Two-factor authentication (or 2FA for short) is an extra layer of security that ensures that the person wanting access to an account is who they say they are. The requestor doesn’t get immediate access to an account by simply entering a user name and password. There is an extra layer of security with an additional step.
 Think of this security option as having a deadbolt as well as a safety chain on your front door. The most visible (to the public) of this security option is, for example, the follow-up text you get in response to typing in your password on a regularly used site that has 2FA. Since the additional request is sent to a trusted secondary contact point like an email or mobile phone, the access is far more secure than if only one layer was in place.
Think of this security option as having a deadbolt as well as a safety chain on your front door. The most visible (to the public) of this security option is, for example, the follow-up text you get in response to typing in your password on a regularly used site that has 2FA. Since the additional request is sent to a trusted secondary contact point like an email or mobile phone, the access is far more secure than if only one layer was in place.
Why this method?
So why rely on this method of security management? Won’t my traditional method of user name plus a password suffice? We’ve already covered earlier why and how to solve the password security dilemma. However, passwords aren’t foolproof because:
- Users tend to use simple or overused and easy-to-guess passwords.
- With multiple accounts users tend to reuse the same passwords and thereby increasing the possibility that their passwords will be discovered (and put multiple accounts at risk).
What does 2FA bring to this security party?
By implementing 2FA, an extra layer is added that, while adding security, doesn’t necessarily add complexity to account access (sign on). It just means users need to have at hand another piece of unique information to gain access to their accounts. This extra information can take the form of a:
- PIN, additional password or answers to a series of secret questions.
- Physical token, credit card or smart phone.
- Software-based token (or one-time passcode or TOTP).
- Push notifications.
- Biometric such as a fingerprint.
With cybercrime threats and awareness growing each day (to the tune of billions of stolen passwords, the leading cause of security breaches), it only makes sense to implement the best and latest alternatives you have available. It is a way to not only secure your internal data but put you in a good light with your clients and customers since it shows a respect for their data.
3T Pro is here to help our clients run productive and efficient companies. For more information or to schedule a review, please contact us.