Security, Tips
Enhancing Cybersecurity for Businesses in Dallas Cybersecurity is a growing concern for small businesses in Dallas. Implementing robust security measures can protect your business from cyber threats. We have been providing Dallas IT support to businesses for 32 years....

Security
Small businesses often operate under the misconception that they are too small to be targeted by cybercriminals. However, this could not be further from the truth. Small businesses need to prioritize cybersecurity now more than ever. Below will highlight the reasons...

Security
Cybersecurity has been making headlines this past year. From the rise in ransomware attacks, to data breaches and more, many companies are realizing that network security is important in almost every industry. For many businesses, investing in reliable and effective...

Security
We’ve all been told our entire lives to be careful what information we put on the internet because it’s important to protect our personal information. So we all just installed a Norton anti-virus program and then went about our day as normal assuming...

Security
Computer viruses and malware attacks have become daily occurrences and more complex and complicated. If you don’t have systems that will protect, defend and respond to these attacks, your business and very livelihood are at risk. Over the past several years,...

Security
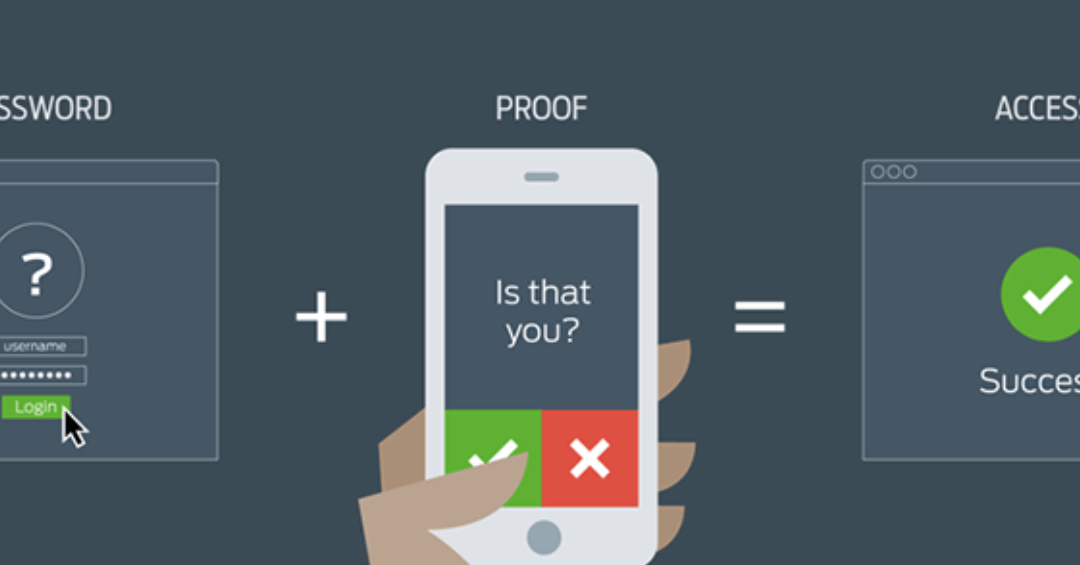
As cybercrime increases, we all need to be doing more pre-emptive pushback on these activities. One of the weapons in this ongoing battle is two-factor authentication. Just what is it and how can I implement it if I need to? What is it? Two-factor authentication (or...