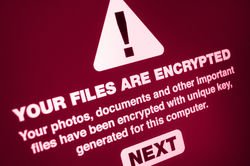

Protecting Your Inbox
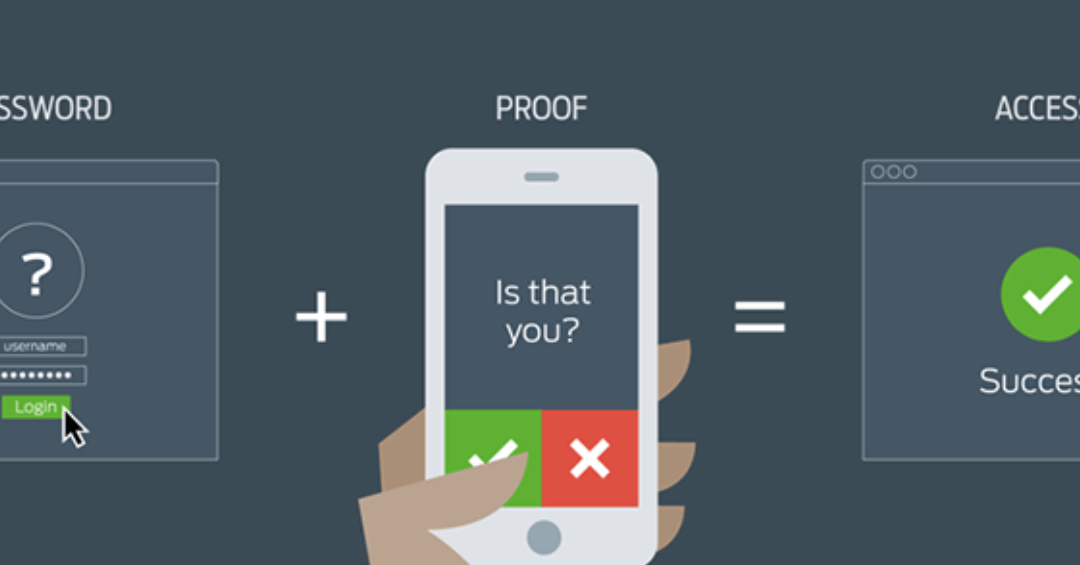
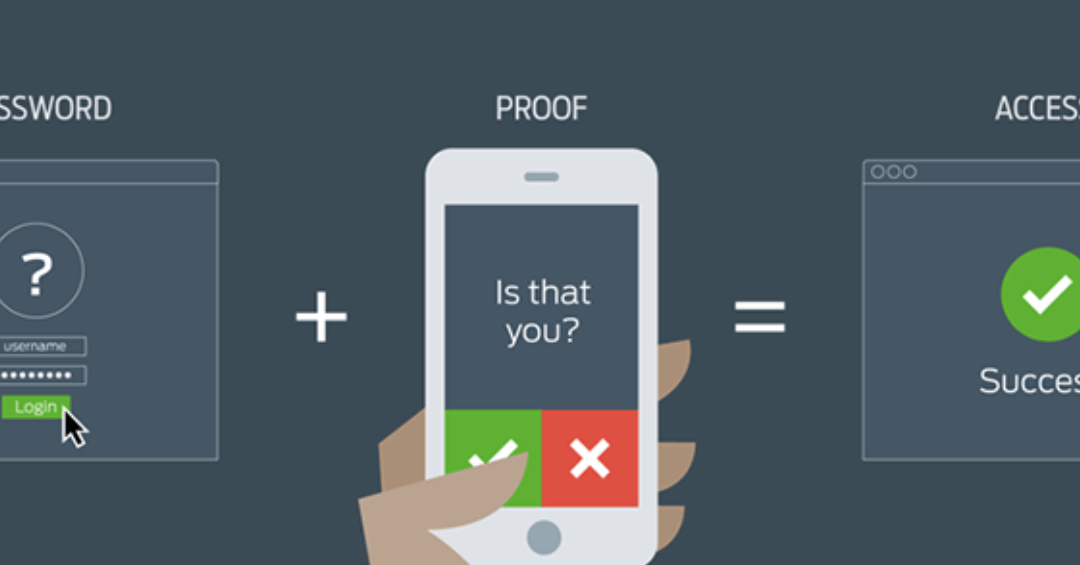
These days, companies’ email systems are one of the most vulnerable places from which a cyber attack can come. this post provides some valuable in formation and solutions relating to how to deal with an attack of this type.

How Big (or Small) Do I Have to Be to Outsource My IT Services?
When is the best time for your company to choose a qualified strategic IT partner? How big do you have to be to take this step?
Does My IT Strategy Really Impact My Bottom Line?
In today’s world, if you don’t rely on information technology (IT) daily, chances are you either don’t’ understand what IT is or you haven’t integrated it into your business as effectively as you could be doing. When PCs started coming into businesses in the early...