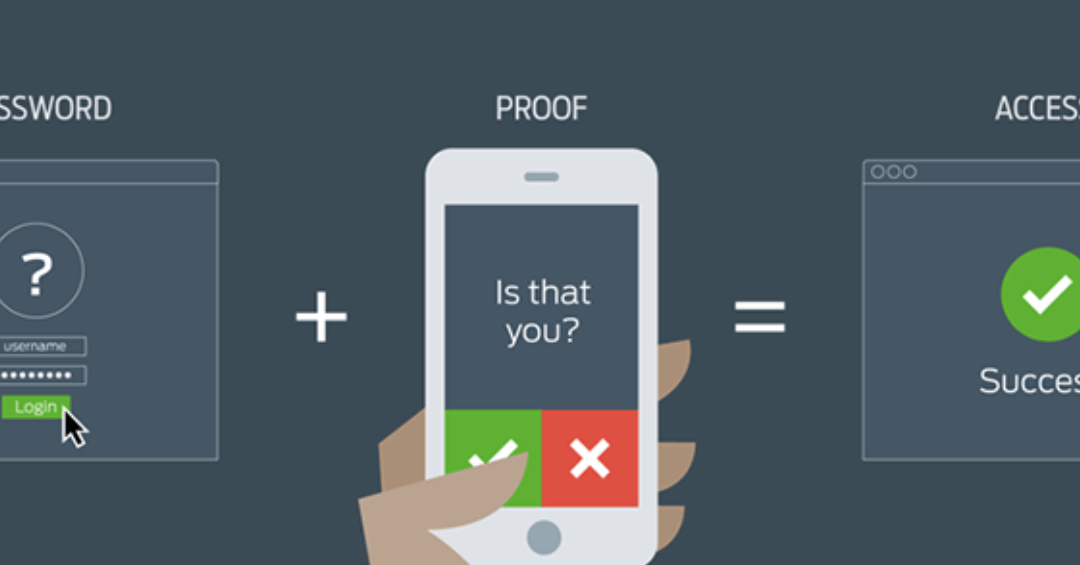
What is Two-Factor Authentication?
As cybercrime increases, we all need to be doing more pre-emptive pushback on these activities. One of the weapons in this ongoing battle is two-factor authentication. Just what is it and how can I implement it if I need to? What is it? Two-factor authentication (or...
Protecting Your Inbox
These days, companies’ email systems are one of the most vulnerable places from which a cyber attack can come. this post provides some valuable in formation and solutions relating to how to deal with an attack of this type.

How Big (or Small) Do I Have to Be to Outsource My IT Services?
When is the best time for your company to choose a qualified strategic IT partner? How big do you have to be to take this step?